How to Start a Career in Ethical Hacking in 2026
A complete roadmap for beginners who want to break into ethical hacking and penetration testing.
Read More
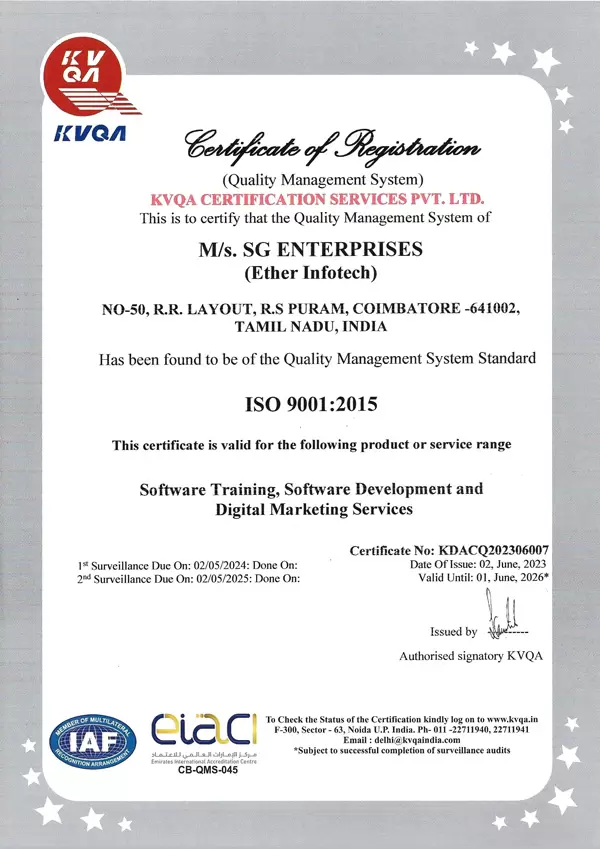
The Ethical Hacking Course in Coimbatore at Ether Infotech is designed to train students and IT professionals to think and act like a hacker — legally and ethically — to identify and fix security vulnerabilities before malicious actors can exploit them. Our hands-on curriculum covers the complete penetration testing lifecycle: Reconnaissance, Scanning, Exploitation, Post-Exploitation, and Reporting, along with specialized modules on web application hacking, network attacks, social engineering, wireless security, and bug bounty hunting. With CEH v13-aligned content and live lab environments using Kali Linux, Metasploit, and Burp Suite, you will graduate as a confident, job-ready Ethical Hacker.
At Ether Infotech, we offer a comprehensive Ethical Hacking Course in Coimbatore that blends real-world hacking tools, live penetration testing labs, and career-driven training. Recognized among the best Ethical Hacking courses in Coimbatore, our program ensures you gain the offensive security skills companies are actively hiring for.
Whether you're a student, fresher, IT professional, or career switcher, this course is structured to make you industry-ready and confident in the field of ethical hacking and penetration testing.
Our training is led by CEH and OSCP certified security professionals who focus on hands-on learning through live attack simulations, CTF (Capture The Flag) challenges, and real-world pen testing case studies. The curriculum emphasizes not just concepts, but how to exploit them — and how to report and fix them professionally.
We also provide flexible learning options to match your schedule — weekday and weekend batches available — so you can upskill without compromising your routine.
With dedicated placement support, resume building, mock interviews, and HR guidance, we prepare you to secure roles as an Ethical Hacker, Penetration Tester, or Security Analyst with confidence.
Take your first step toward a rewarding career by joining our Ethical Hacking course in Coimbatore today.
3–5 months with flexible learning options (weekdays/weekends).
Kali Linux, Metasploit, Burp Suite, Nmap, Wireshark, Nessus, SQLmap, Hydra, Aircrack-ng.
Practice on live vulnerable machines, CTF challenges, HackTheBox & TryHackMe labs.
Learn from CEH v13 & OSCP certified professionals with real pen testing experience.
Resume building, portfolio projects, mock interviews & direct job referrals to 50+ companies.
Master Recon, Scanning, Exploitation, Post-Exploitation, and professional report writing.
Exploit OWASP Top 10 vulnerabilities — SQLi, XSS, CSRF, IDOR — using Burp Suite.
Execute MITM attacks, ARP poisoning, sniffing, and DNS spoofing on live networks.
Build and deliver payloads, maintain persistence, and escalate privileges using Metasploit.
Hunt real vulnerabilities on platforms like HackerOne and Bugcrowd to earn rewards.
Ether Infotech is the premier training institute in Coimbatore, offering top-notch courses in Ethical Hacking, Cybersecurity, Python training, Java training, Digital Marketing, and Data Science. Our industry-relevant curriculum, CEH-certified trainers, and live penetration testing labs ensure you graduate with practical, job-ready offensive security skills. We provide comprehensive support including career counseling, placement assistance, and strong industry connections across IT, BFSI, and cybersecurity consulting firms. Flexible online and offline learning options cater to diverse schedules. Join Ether Infotech to advance your career with the best Ethical Hacking training in Coimbatore.
Ethical Hacking — also known as Penetration Testing or White-Hat Hacking — is the authorized practice of bypassing system security to identify potential data breaches and threats in a network. The company that owns the system or network allows the Ethical Hacker to perform such activities in order to test the system's defenses.
Unlike malicious hackers, Ethical Hackers document their findings in detailed reports and work with organizations to remediate vulnerabilities. They use the same tools and techniques as black-hat hackers — Metasploit, Burp Suite, Nmap, and Wireshark — but operate with explicit legal permission and follow a strict professional code of conduct.
An Ethical Hacking course opens strong career opportunities across IT security firms, startups, BFSI, government cybercells, defense organizations, and multinational corporations looking to protect their digital assets.
With cybercrime costs projected to reach $10.5 trillion annually by 2025, organizations are investing heavily in offensive security talent. Ethical Hackers and Penetration Testers in India command salaries ranging from ₹5–8 LPA at entry level to ₹25+ LPA at senior positions.
The growing IT and manufacturing ecosystem in Coimbatore, combined with India's booming Bug Bounty culture, creates excellent career and freelance opportunities in the ethical hacking field.
At Ether Infotech, we provide flexible and affordable training options designed for different learning needs. Whether you're a student, working professional, or job seeker, our Ethical Hacking Course in Coimbatore offers the perfect balance of quality training, practical lab exposure, and career-focused learning.
Ideal for students and working professionals who prefer a steady and flexible learning schedule.
Best for job seekers who want fast-track training with real-time labs and live hacking projects.
Our Ethical Hacking Course in Coimbatore is designed with the following key objectives in mind
Understand hacking phases, types of hackers, legal frameworks, and the CEH methodology used by security professionals worldwide.
Master passive and active information gathering using OSINT, Maltego, Shodan, theHarvester, and Google Dorking techniques.
Use Nmap, Nessus, and Netcat to discover open ports, services, OS fingerprints, and enumerate network targets effectively.
Exploit vulnerabilities using Metasploit, custom payloads, privilege escalation, lateral movement, and persistence techniques.
Attack web applications using Burp Suite, exploit OWASP Top 10, and crack WEP/WPA2 wireless networks using Aircrack-ng.
Complete exam-aligned practice tests, mock labs, and guided Q&A sessions to confidently clear the CEH v13 certification exam.
Completing our Ethical Hacking Course in Coimbatore at Ether Infotech opens doors to high-demand career opportunities in the rapidly growing offensive security industry.
Conduct authorized security assessments to find and exploit vulnerabilities in client systems and networks.
Simulate advanced persistent threats and multi-stage attack campaigns to test organizational defenses.
Specialize in finding and exploiting vulnerabilities in web applications, APIs, and cloud-hosted services.
Earn rewards by discovering and responsibly disclosing vulnerabilities through platforms like HackerOne and Bugcrowd.
Apply offensive security knowledge to detect, analyze, and respond to threats in Security Operations Centers.
Deliver end-to-end Vulnerability Assessment & Penetration Testing engagements with professional reports for clients.
Ethical Hackers and Penetration Testers are among the most sought-after security professionals across IT, BFSI, government cybercells, defense, healthcare, and multinational organizations. With cybercrime costs projected at $10.5 trillion annually, companies worldwide are investing heavily in offensive security talent. Our training prepares students with real tools, real labs, and real-world experience to secure high-paying ethical hacking careers.
Comprehensive Ethical Hacking Training Curriculum – CEH v13 Aligned






























We build ethical hacking careers with practical skills, real lab projects, and placement support.
CEH v13-aligned curriculum with OSCP preparation and live hacking lab environments.
Real-time hacking labs with HackTheBox, TryHackMe, CTF challenges, and vulnerable VMs.
Mock interviews and placement assistance to crack ethical hacking and pen testing job interviews.
Hands-on hacking projects with 100% dedication and expert certified guidance.
Learn to earn by hunting bugs on HackerOne and Bugcrowd with expert mentorship and live walkthroughs.
Trusted by universities for ethical hacking internships and campus security placement drives.
Explore career tips, technology updates and ethical hacking industry insights.
A complete roadmap for beginners who want to break into ethical hacking and penetration testing.
Read More
Compare the two most respected ethical hacking certifications to find the best fit for your career goals.
Read More
Discover how Indian ethical hackers are earning lakhs annually through bug bounty programs in 2026.
Read More